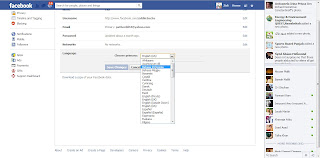
Facebook is the most used Social network ever. Almost everybody has a Facebook account. In fact one can get loads of information about somebody from their Facebook account. When it comes to privacy, Facebook might not be the best platform. As it is said that there are all kinds of workaround for everything, therefore there is a workaround for removing the middle name and last name from your Facebook profile as well.
In order to create a Facebook account the user has to pass through various security checks, this is because Facebook does not want any scam or fake profile. To ensure this, one of the measures which Facebook takes into consideration is that it does not allows anybody to miss out the last name. Hence one cannot create his/her profile only by first name and middle name, it is mandatory to fill out your last name as well.
. See the steps below if you want to hide your last name from your Facebook profile, and believe me it’s quite simple.
Remove Your Last Name from Facebook :
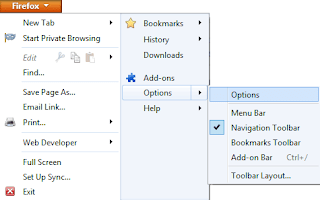
1. If you have Mozilla Firefox installed then run it, else download it.
2. Now go to Firefox > Options > Options.
P.S. This trick is for those people those who need to hide their last name, this can be due to any reason like security or any other. But anyone can remove the last name and show that they can do it and their friends can’t.